News
WannaShift to Monero
Neutrino Research Team - 2017-09-01, 00:02
Intro
Between March and May 2017 hundreds of thousands of machines were infected by a ransomware known as Wannacry. In particular with the second wave of infection the Hackers used tools stolen by the National Security Agency to exploit a flaw in Microsoft Windows to spread the ransom. It was reported worldwide as one of the most important massive cyber-attack in recent times. Even if the media paid most of the attention on the last version of Wannacry, security researcher were able to identify different versions of this malware[1]. Based on the Wannacry versions identified by Fortinet we started to follow the bitcoins collected by the ransomware authors.
Wannacry 1.0
Two bitcoin addresses[2] appear to belong to Wannacry 1.0:
- 1QAc9S5EmycqjzzWDc1yiWzr9jJLC8sLiY
- 15zGqZCTcys6eCjDkE3DypCjXi6QWRV6V1
These two addresses received 19 incoming transactions for a total of 4.69 BTC.
On July 19th, h. 08:18 UTC, a first outgoing transaction was originated by the Wannacry 1.0 wallet. The transaction moved 0.1 BTC to the address 15LYiRgE2WNsb6iwFQC9UZtayYTDYucNyD. Additional two transactions were performed to empty the wallet in the early hours of July 20th.
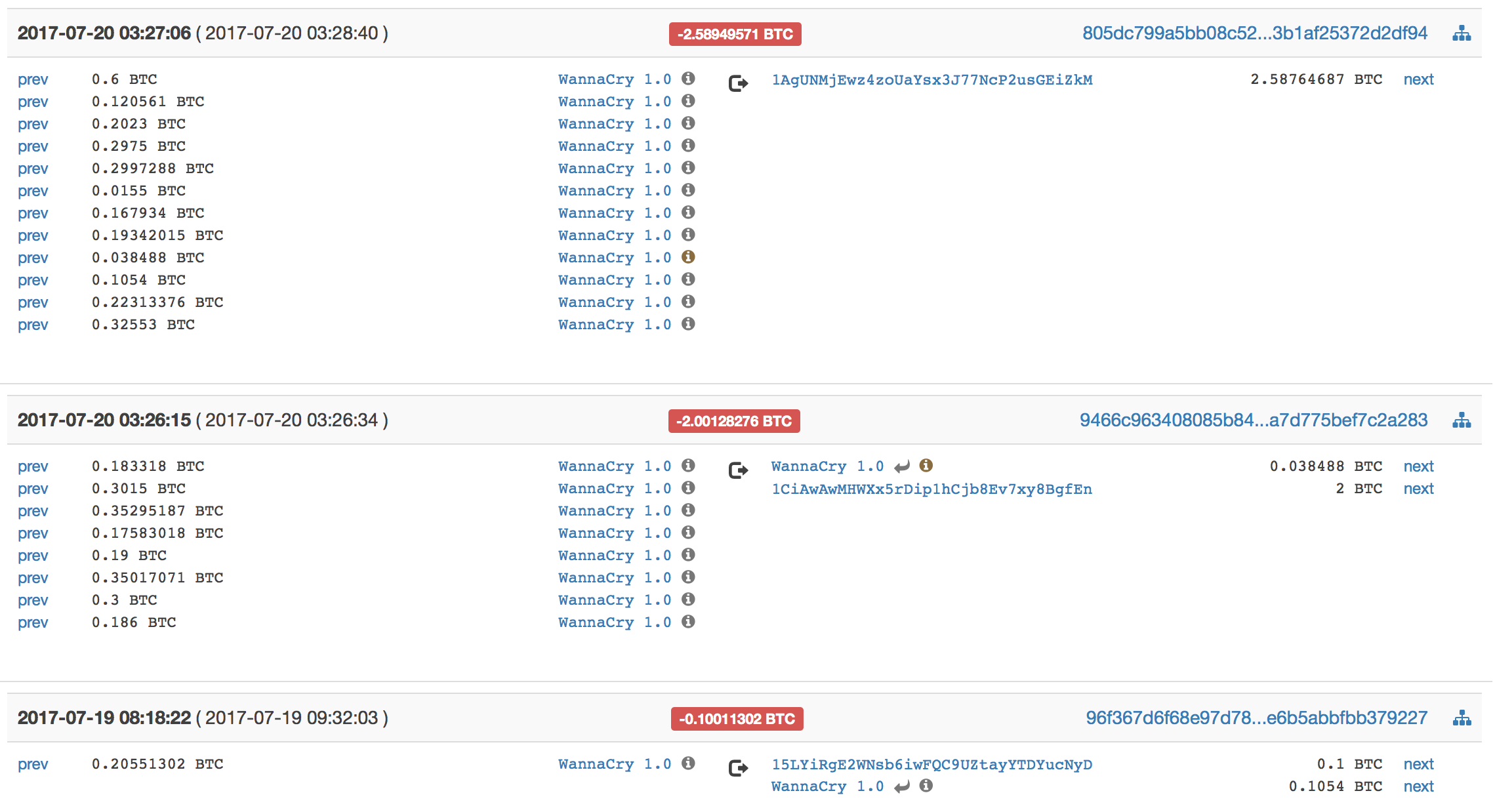
We proceeded with the outgoing transactions analysis to spot the actual destinations of the payments. After 1 single hop, the bitcoins are moved to bitcoin addresses belonging to Shapeshift[3], a well-known online exchange provider that allows user to swap among different crypto-to-crypto pairs.
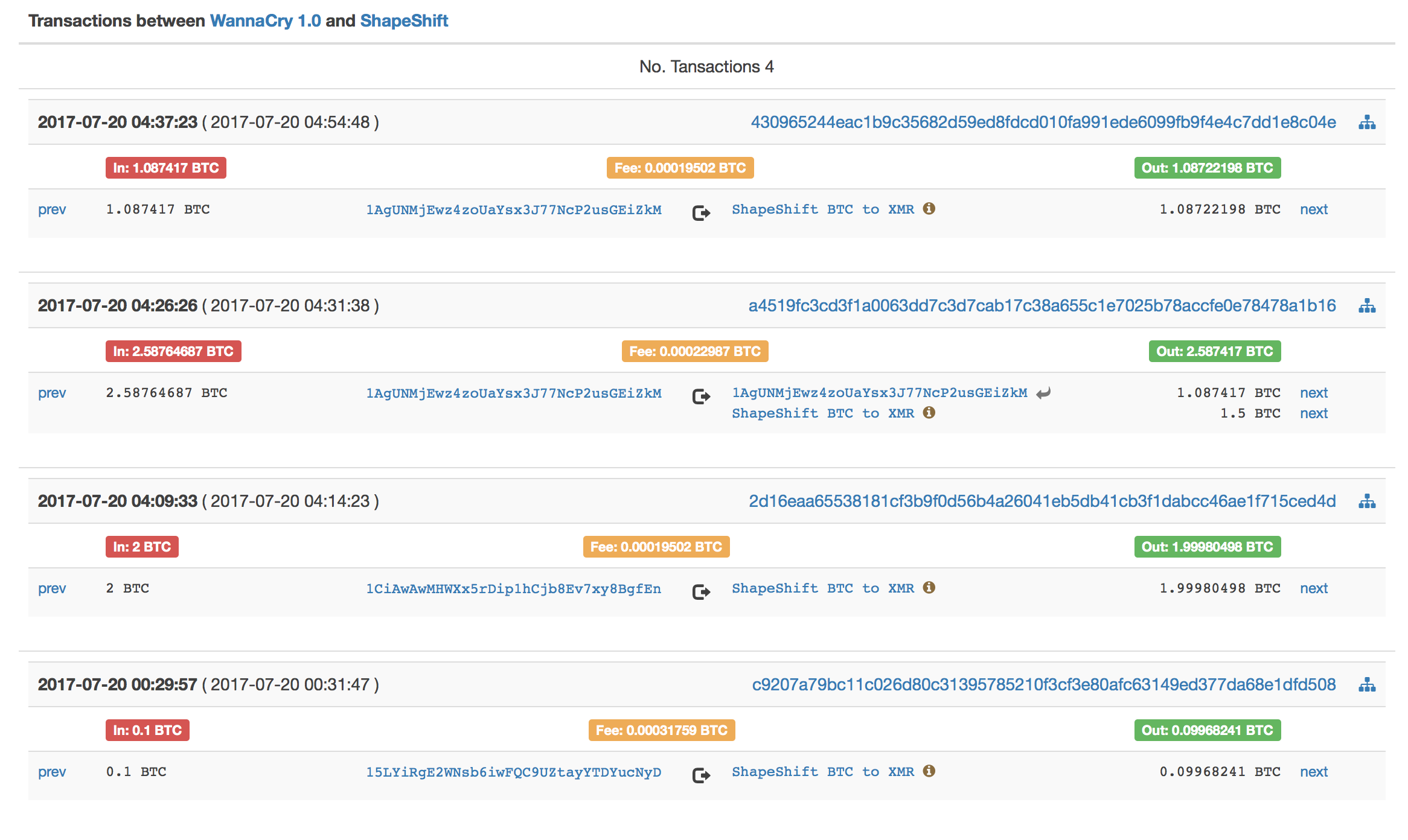
From the graph below it is easy to notice that the whole amount exiting from the Wannacry 1.0 wallet (orange box on the top) ends up, after 1 hops, into the Shapeshift wallet (orange box at the bottom) with four different transactions, listed below.
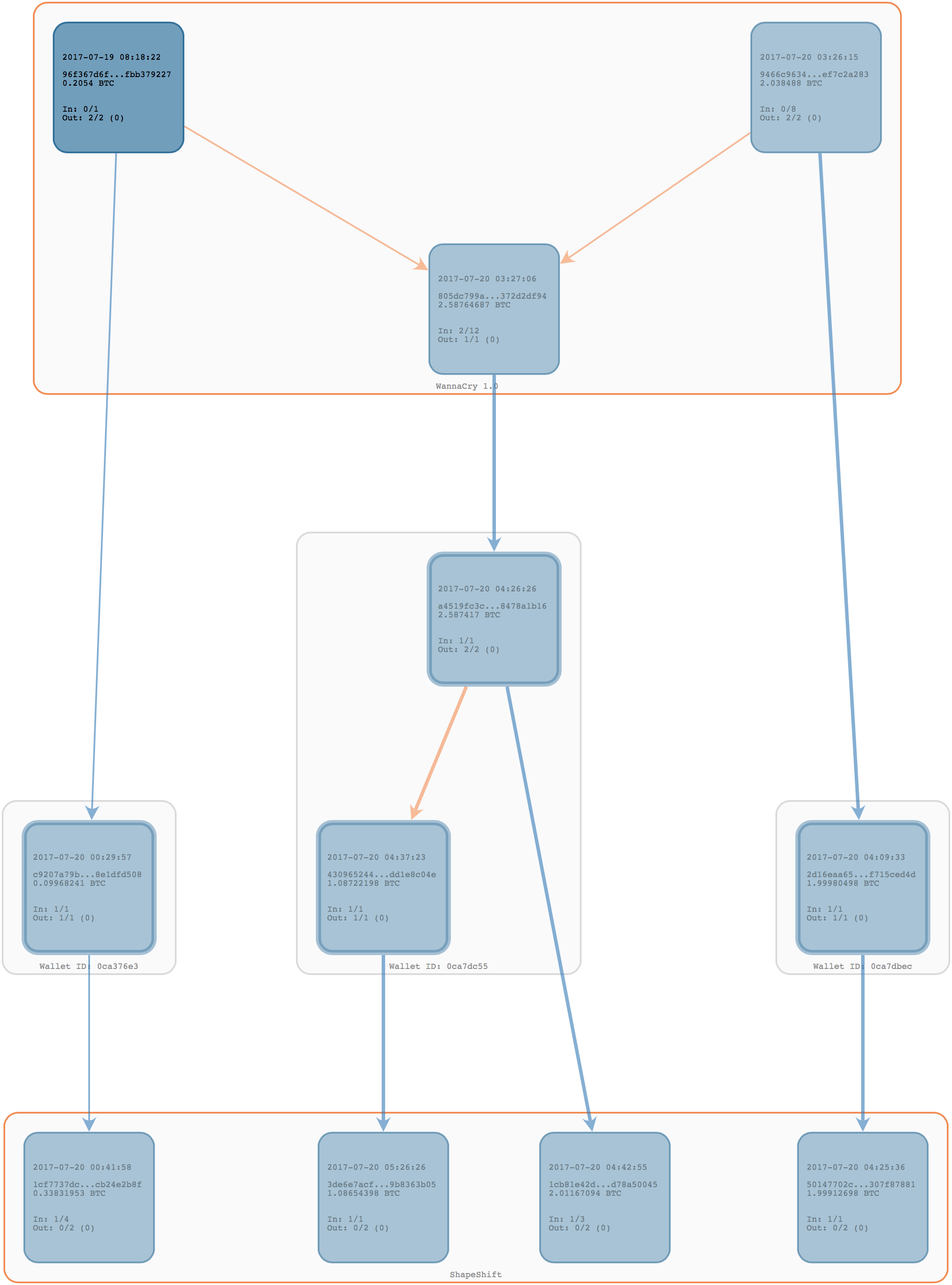
Thanks to P-Flow capabilities, we were able to identify the crypto-to-crypto pairing chosen by the criminals: the four transactions swapped BTC/XMR, Bitcoins to Monero[4], another popular cryptocurrency well known for its wide adoption on darknet markets.
It appears that the swap was performed splitting the bitcoins in 4 transactions sending bitcoins to the following Monero address:
49rJThdEQrjBiBKwvGDNpH28uWstwAMvVSYez3qYjkNWH4A8CbKRYnU82Hzmrs2a31NyDEb59hC6SBTekUsdgsMm28QxdDH
The total amount of bitcoins converted in Monero is equal to: 296,26 XMR.
Wannacry 2.0
The second version of Wannacry infected hundreds of thousands of machine worldwide including hospitals and enterprises. A bitcoin payment of about 300 USD was asked to decrypt the files: on August 3rd, the Wannacry group started moving the funds.
Three bitcoin addresses were identified as belonging to the Wannacry 2.0 wallet used to receive the ransom payments: 13AM4VW2dhxYgXeQepoHkHSQuy6NgaEb94115p7UMMngoj1pMvkpHijcRdfJNXj6LrLn12t9YDPgwueZ9NyMgw519p7AA8isjr6SMwA total of 333 incoming transactions for a total of almost 51.93 BTC were collected.
On August 3rd, h. 03:06 UTC, a first outgoing transaction was registered on the blockchain. The transaction moved 8.73 BTC; the wallet was emptied in a few minutes in five additional transactions.Analyzing the chain, we were able to associate the spending transactions to 2 main different beneficiary: Shapeshift and Changelly[5].
Part of Wannacry 2.0 funds were moved to Shapeshift, the same service provider the author of Wannacry 1.0 used to move those Bitcoins. In particular we were able to identify 8 different transactions that were used to swap bitcoin originated from the Wannacry 2.0 wallet to Shapeshift.
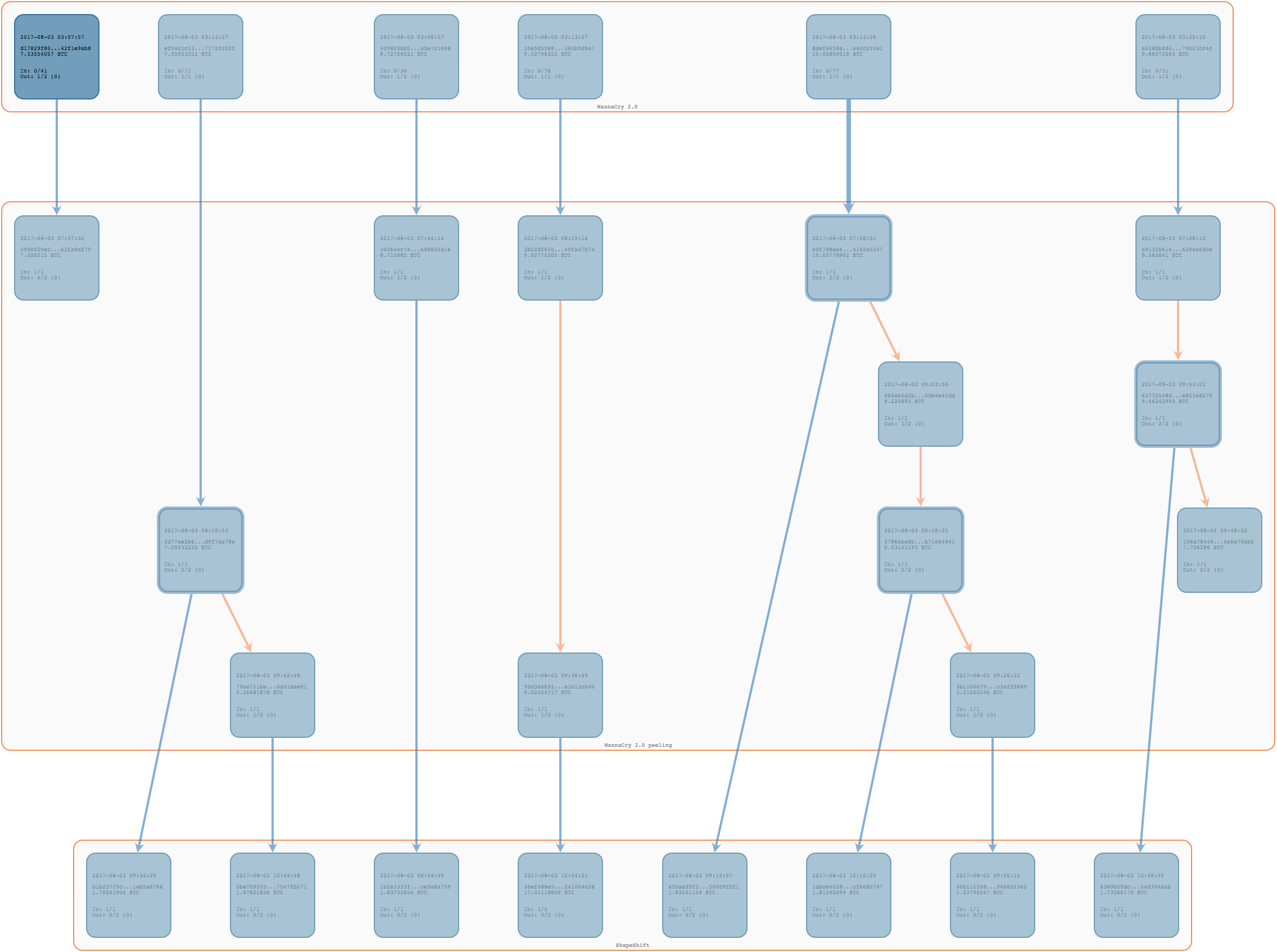
The 8 transactions that moved funds to Shapeshift happened between Aug. 3rd 07:44 UTC time and 09:53 UTC. It is interesting to note that the author of Wannacry used another wallet to manage the peeling process, named "Wannacry 2.0 peeling" in the graph above.
The total amount of bitcoins moved to Shapeshift is equal to 13,53 BTC and they were shifted each time to the same Monero address:
46jECbnrkJTUks7Fg5YtwShdUCiwUwEEZJtJBhKLK4GBWfBX7PLrYBuWR9zhzos5uQ1uXGUgFpGCSBR5o651pL5ERxmwqHu
totalling 820,8 XMR.

Another interesting pattern is about the Bitcoins that ended up into Changelly, a known online exchange with similar functionalities as Shapeshift. We identified 11 different transactions that were swapped on Changelly.
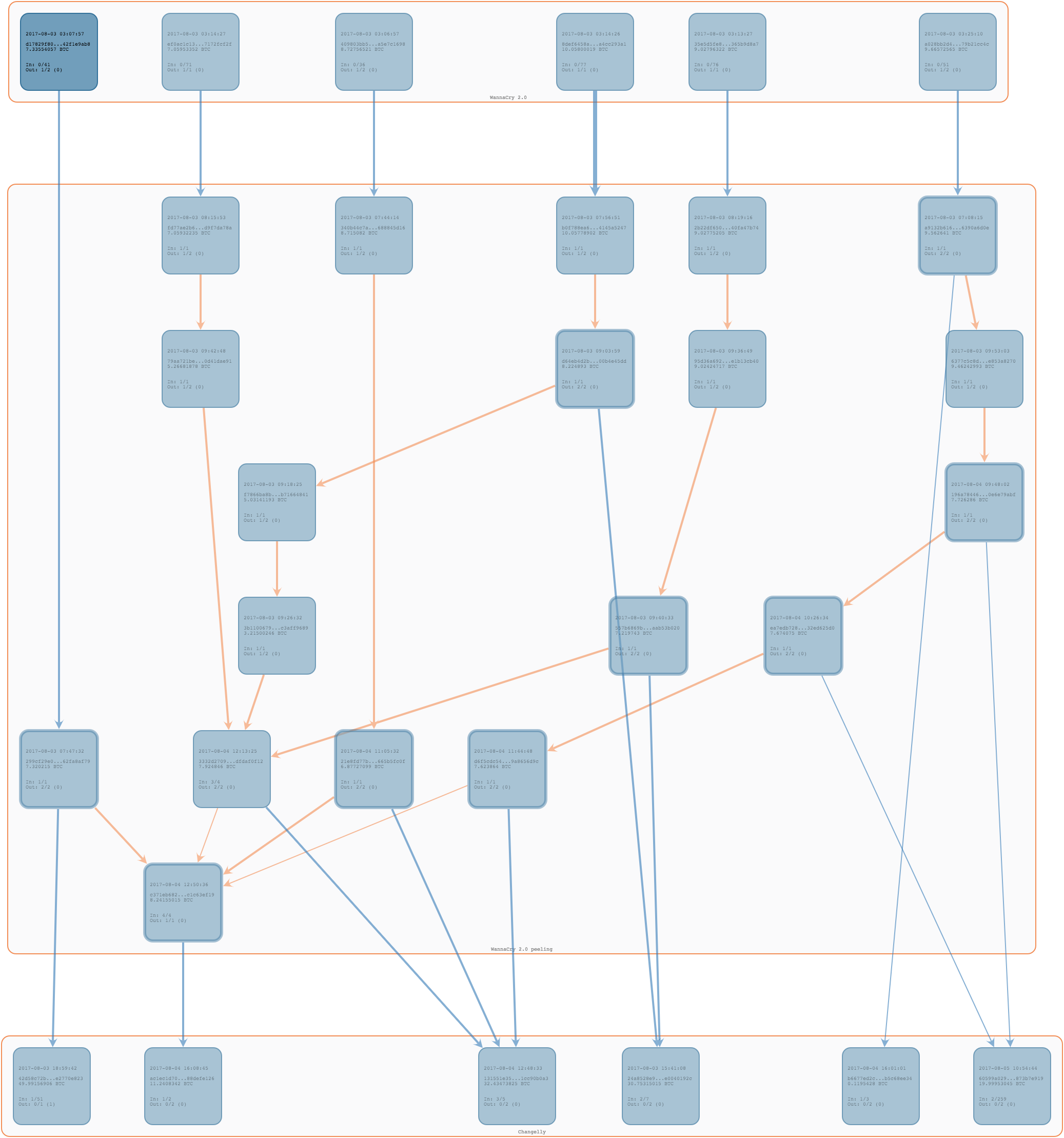
About 38.33 BTC were swapped on Changelly, probably receiving again Monero.
The very first transaction to Changelly moved on August 3rd at 07:08am UTC and it was 0.1 BTC worthy (maybe only a small test).
The "Wannacry 2.0 peeling" wallet was emptied on August 4th at 12:50 UTC with its last transaction to Changelly.
Changelly does not manage its own wallet, it directly used different exchanges to perform the swaps,. We were able to identify that the exchange used for this conversion was HitBtc[6].
Conclusions
Based on the evidence collected we were able to highlight spending patterns used by both hackers of Wannacry 1.0 and 2.0 and we were able to spot some similarities
- In both cases the authors swaped Bitcoins into Monero.
- Wannacry 1.0 used exclusively Shapeshift to swap bitcoin and send them to a single Monero address in 4 different transactions; a similar behavior was recognized in Wannacry 2.0: the 8 Shapeshift transactions swapped the Bitcoins to the same monero address.
- Plausibly, due to the higher volume involved and limit imposed by Shapeshift on swap transactions[7], the author of the ransomware decided to look for another provider -Changelly in this case - to accelerate the swap activities. Also to note, that after the first shifts ShapeShift started blacklisting the Wannacry addresses.
According to the behaviour of the two cases, we consider plausible that the same group of people is laundering the Bitcoins collected with the two Wannacry campaign.
[1] https://blog.fortinet.com/2017/05/15/wannacry-evolving-history-from-beta-to-2-0
[2] A third bitcoin address - 13JfxwBKfL8VcXgjEuVFKRjh44EvL3Lee4 - is a change address of a spending transactions.
[4] https://en.wikipedia.org/wiki/Monero_(cryptocurrency)
[7] The amount of bitcoin that can be shifted on a single transaction is generally included in a range of 1 to 2 BTC.